How to harden your private VM by distro-morphing it into Kicksecure
What is Kicksecure? Kicksecure is a free and open-source Linux distribution designed to provide a highly secure computing environment. It is built on a hardened version of Debian, implementing a defense-in-depth security model that protects against various types of malware and attacks.
Reasons to use Kicksecure
- Enhanced Security Features:
Kicksecure is designed with a strong focus on security, incorporating various hardening techniques such as kernel hardening, user account isolation, and application-specific restrictions.
- Privacy Protection:
All updates and software installations are routed through the Tor network, ensuring that user identities and IP addresses remain anonymous.
- Lower Attack Surface:
Kicksecure minimizes potential vulnerabilities by not having open server ports or unnecessary services running by default.
- User -Friendly Experience:
The operating system is designed to be accessible, with many applications available in their apt repositories and configured for immediate use, such as the tor browser.
- Compatibility with Virtualization:
Kicksecure supports various virtualization options, allowing users to run it in a virtual machine.
- Free and Open Source:
As an open-source project, Kicksecure allows users to review, modify, and redistribute the source code.
Kicksecure is important in many scenarios. It is ideal for individuals handling sensitive data, such as personal or financial information, as its robust security features protect against data breaches and unauthorized access. Journalists, activists, and whistleblowers can maintain anonymity while communicating, safeguarding their identities from surveillance. Users accessing public Wi-Fi can rely on Kicksecure for secure browsing, reducing the risk of data interception. Running Kicksecure in a virtual machine helps contain potential malware threats, protecting the primary operating system. Additionally, developers and researchers can create a secure environment for security tools and cybersecurity research. Kicksecure also serves as an educational resource, offering documentation and community support for users looking to enhance their security knowledge. Its hardened configuration defends against brute force attacks, making it suitable for securing sensitive accounts. Overall, Kicksecure is essential for anyone prioritizing security, privacy, and anonymity in their digital activities. For more details on why you should use kicksecure, check out their official website.
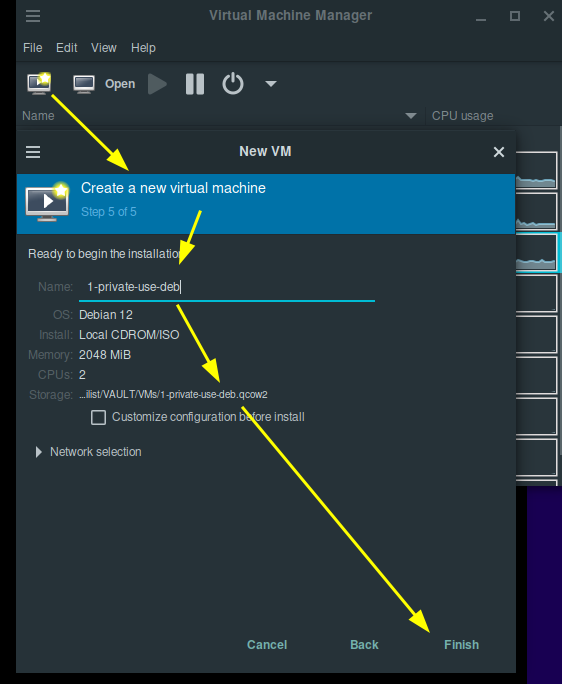
Now let's setup Kicksecure in the private VM, by distro-morphing the Debian guest OS into a Kicksecure guest OS. First,we need to create a new group called console. Then add the your user to the console group
sudo addgroup --system console
sudo adduser "your_username" console
After that,we need to install console related packages.
sudo apt install console-data console-common kbd keyboard-configuration
Now, we will install extrepo to get the kicksecure APT repository. We will also enable the repository
sudo apt install extrepo
sudo extrepo enable kicksecure
Next step is to download the kicksecure packages. Note that this will install a desktop environment(Xfce) and other applications
sudo apt install kicksecure-xfce-host
Finally, we need to enable the Kicksecure APT derivative.list in /etc/apt/sources.list.d/derivative.list
sudo repository-dist --enable --repository onion
This command will generate derivative.list file.

Disable the extrepo kicksecure APT repository. This is to avoid a duplicate Kicksecure repository.
sudo extrepo disable kicksecure
That's it! A quick reboot will apply all the new settings and configurations.
sudo reboot
Changes after reboot
New GNU GRUB menu

sdwdate to synchronize the system clock with time servers over the Tor network for better anonymity.

System Integrity Checks

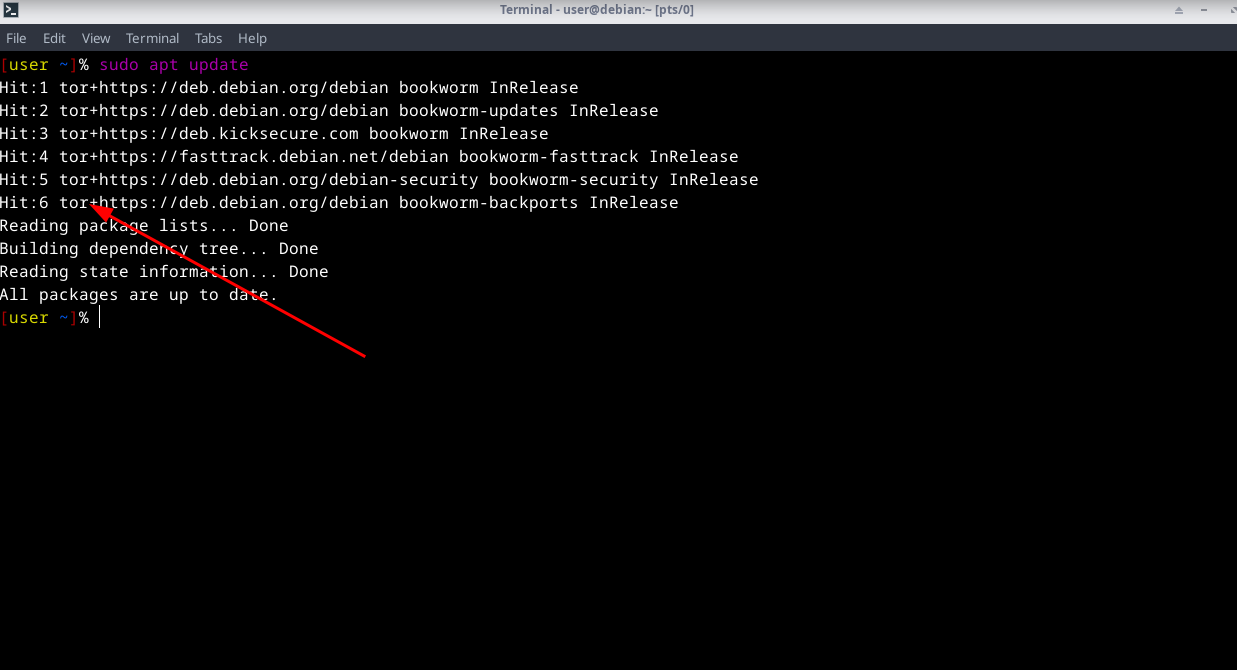
System updates over Tor
In conclusion,Kicksecure offers a robust solution for security and privacy, built on a hardened Debian foundation. Users can confidently operate within a Kicksecure VM, ready for private use in today’s complex digital landscape.